How OpsFabric works
February 12, 2026 · 5 min read · Vedran Lebo
OpsFabric describes itself as an infrastructure data engine. This post shows what that means in practice: what it collects, how fast, and why the numbers matter.
If you're evaluating OpsFabric or just curious about what it actually does, this is for you.
One command, multiple audit domains, under four seconds
OpsFabric fans out commands to every host in your fleet simultaneously. Each host executes locally and returns structured data: no sequential round-trips, no orchestration loops, no polling.
A full fleet audit across 13 hosts completes in 3.7 seconds. That's 3,832 structured data points across multiple audit domains, collected in parallel:
| Domain | Data points | What's collected |
|---|---|---|
| Host info | 208 | OS, CPU, RAM, uptime, IPs, kernel, architecture |
| Services | 2,888 | Running services, status, PID, memory, uptime |
| User accounts | 353 | Local users, groups, shells, sudo access |
| System health | 169 | CPU, memory, disk, load average, network I/O |
| Open ports | 99 | Listening ports, protocols, PIDs, processes |
| Cron jobs | 58 | Scheduled jobs, schedules, commands |
| Firewall rules | 54 | iptables/nftables/firewalld rules and chains |
| Certificates | 3 | TLS/SSL certs, expiry dates, issuers |
This isn't a scheduled batch job that runs overnight. It's on-demand, interactive, and the results stream into the UI as each host responds.
Everything is structured data
Every data point OpsFabric collects is structured, typed, and queryable. Not log lines. Not free-text output piped through grep. Structured records with consistent schemas across every host in your fleet, regardless of distribution or package manager.
This is what makes Fleet Search possible. When you query "which hosts have ports open above 1024" or "which services are consuming more than 500MB of memory", the answers come back in seconds because the data is already normalized and indexed.
The agent: open source and auditable
The agent running on your managed hosts is open source. You can inspect the code, audit what it does, and verify what it collects. No black box binary phoning home to a vendor's cloud.
The agent has a minimal footprint, well under 100MB of memory at rest. It maintains a persistent connection initiated from the host side, so no inbound ports need to be opened on your managed nodes.
All business logic runs locally on each host. When OpsFabric collects host info, scans for patches, or audits firewall rules, the work happens on the host itself and returns structured results. There's no central server parsing command output or running sequential SSH sessions.
Real-time streaming, not batch polling
When you trigger an operation, a patch scan, a service audit, a compliance check, results stream back as each host completes. You see hosts appear in the results table one by one, in real time.
For a 20-host fleet, a full patch scan completes in under 5 seconds. A host sync that collects OS metadata, hardware info, network configuration, and reboot status returns in under 200 milliseconds per host, all executed in parallel across the fleet.
This changes how you interact with your infrastructure. Instead of scheduling a scan for tonight and reviewing results tomorrow, you scan now and act now.
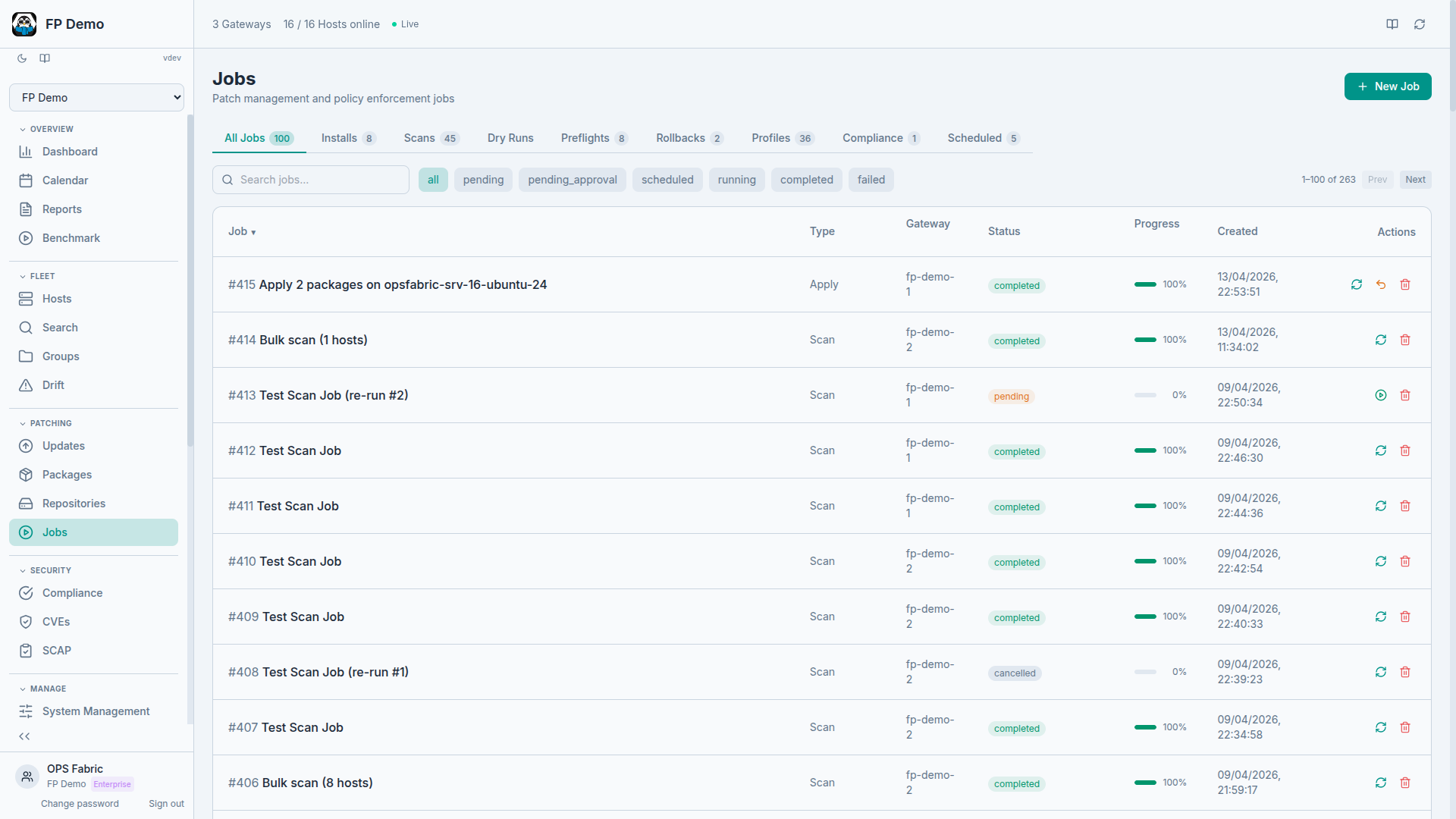
Patch management with full audit trail
Every action taken through OpsFabric is recorded:
- Who initiated the action
- What was targeted (which hosts, which packages)
- When it happened
- What changed (package versions before and after)
- Whether it succeeded (per-host status)
Rollback is built in. When a patch job runs, the system captures package deltas and preserves the ability to revert. If an update breaks something, you roll back to the previous state with a single action, not a midnight SSH session.
CVE intelligence and SCAP compliance
OpsFabric maps installed packages to known vulnerabilities using the OSV.dev database. Every CVE affecting your fleet is tracked with CVSS scores, severity ratings, and affected hosts. You can see which hosts are exposed, which CVEs are most critical, and accept risk on specific vulnerabilities when appropriate.
For formal compliance, OpsFabric runs SCAP (Security Content Automation Protocol) scans against industry benchmarks: CIS, STIG, PCI-DSS, HIPAA, and more. Results are structured, per-host, and reportable. Compliance stops being a quarterly scramble and becomes a live dataset you query anytime.
SCAP remediation: from finding to fix in one click
Most compliance tools stop at telling you what failed. OpsFabric goes further: every SCAP finding is matched to a ready-made remediation directive. When a CIS rule fails, you see exactly what needs to change and can add the fix to a State Profile with one click.
Currently over 100 CIS Level 1 rules have automated remediation built in. Select the failed findings you want to fix, add them to a state profile, run a dry run to preview the changes, then enforce across your fleet. For rules that don't yet have automation, OpsFabric shows the exact shell commands and guidance from the benchmark so you know precisely what to do.
The result: compliance scans and remediation live in the same platform. Find a problem, fix it, rescan, verify. No spreadsheet handoffs between the scanning team and the engineering team.
Fleet Search
Fleet Search is the query interface to all this data. It supports multiple filter domains with AND/OR connectors:
- OS family, version, architecture
- Package name and version (installed or available)
- Service name and status
- Open ports and protocols
- Environment, group, gateway
- Patch status and vulnerability exposure
- Host metadata (hostname, IP, uptime, reboot status)
Queries return in seconds against live data. Saved searches let you bookmark cohorts you care about: "all CentOS hosts with OpenSSL below 3.0.8" or "all hosts in production with pending security updates."
Not just auditing. Management.
Everything above describes the observation side: collecting data, querying it, reporting on it. But OpsFabric also manages and enforces fleet state.
State Profiles let you declare desired state across multiple domains (users, services, packages, cron jobs, firewall rules, kernel parameters, and more) and enforce it fleet-wide. Dry runs preview what would change without touching anything. Drift detection shows where hosts have diverged from the baseline. Every enforcement action gets the same audit trail as every scan.
The same platform that tells you "14 hosts are missing the deploy user" also fixes it. The same platform that finds unauthorized firewall rules also enforces the correct ones. Observation and management in one place, with the same speed and the same audit trail.
What the numbers mean
The performance characteristics aren't academic. They change what's practical.
When a full fleet audit takes 3.7 seconds instead of 30 minutes, you stop scheduling audits and start running them whenever you need answers. When patch scans are interactive instead of batch, you stop treating patching as a weekly ceremony and start treating it as a continuous practice.
When every action has an audit trail and every host's state is queryable, compliance stops being something you prepare for and starts being something you derive from data that already exists.
Next in the series: Beyond auditing: managing fleet state with State Profiles, drift detection, and fleet-wide enforcement.