NIS2 and DORA compliance: what auditors actually ask for
March 19, 2026 · 7 min read · Vedran Lebo
If your organization falls under NIS2 or DORA, you already know the broad strokes: risk management, incident reporting, access control, vulnerability management, business continuity. The directives are clear on what you must achieve. They're less clear on how to prove you actually did it.
That's where most teams get stuck. Not on understanding the requirements, but on producing the evidence. When an auditor walks in and asks "show me your patch compliance rate for the last 90 days," you need an answer that isn't a spreadsheet someone updated last month.
Compliance tooling, not a compliance solution
Let's be honest about what OpsFabric is and isn't.
OpsFabric is not a GRC platform. It won't write your risk register, manage your vendor assessments, or generate board-level compliance reports. For that you need tools like Vanta, Drata, or ServiceNow GRC.
OpsFabric is not a SIEM. It won't detect intrusions, correlate security events, or send breach notifications. For that you need Splunk, Elastic, or Wazuh.
What OpsFabric does is sit between your compliance policies and your infrastructure. You decide the rules. OpsFabric enforces them across your fleet and generates the audit evidence that proves you did.
Your GRC platform tells you what controls you need. OpsFabric makes those controls real on every server and produces the proof. That's the gap most teams struggle with, and it's exactly where OpsFabric fits.
What auditors actually ask for
We've talked to teams going through NIS2 and DORA assessments. The questions auditors ask are remarkably consistent. Here's what they want to see and how OpsFabric provides the answer.
"Show me your asset inventory"
NIS2 Article 21(2)(i) explicitly requires "asset management," while DORA Article 8 requires organizations to "identify all information assets and ICT assets" and "maintain relevant inventories." Not a spreadsheet from last quarter. A live, accurate list of every system, its OS version, installed software, and network exposure.
OpsFabric's fleet management provides this automatically. Every managed host reports its hostname, IP addresses, OS family and version, kernel version, installed packages, running services, open ports, user accounts, and firewall rules. Updated in real time or on a schedule you define.
"How do you manage vulnerabilities?"
Both directives require a structured vulnerability management process. OpsFabric's CVE intelligence correlates every CVE from OSV.dev against every installed package across your fleet. Each vulnerability gets a CVSS severity score, affected host count, and fix-available status. You can filter by severity, by host, by package, and drill down to which specific servers are exposed.
"How quickly can you patch critical vulnerabilities?"
NIS2 emphasizes timely remediation. DORA requires documented patch management processes with defined timelines. OpsFabric's job history provides timestamped evidence of every patch operation: when the scan ran, when the apply was approved, when each host completed, and what changed. Approval workflows and maintenance windows provide the process controls auditors look for.
"Are systems configured to a security baseline?"
This is where SCAP compliance comes in. OpsFabric runs CIS, STIG, PCI-DSS, and HIPAA benchmarks against your fleet and produces compliance scores per host, per benchmark, with trending over time. When a rule fails, one-click remediation matches the finding to a fix, adds it to a state profile, and enforces it across your fleet.
103 CIS Level 1 rules have automated remediation built in. For the rest, OpsFabric provides the exact shell commands and guidance from the benchmark.
"How do you detect configuration drift?"
Both NIS2 and DORA require ongoing monitoring, not point-in-time checks. OpsFabric's drift detection compares the current state of each host against its assigned state profiles and flags deviations. Someone manually opens a port, adds a user, or disables a service? The platform knows, and you can remediate from the same screen.
"Who has privileged access?"
Access control is a core requirement under both directives. OpsFabric audits user accounts across your entire fleet: who exists, which groups they belong to, who has sudo access, and which SSH keys are authorized. State profiles can enforce that specific users must (or must not) exist, with specific permissions, across every host.
"Show me your change management controls"
DORA Article 9 specifically requires documented change management. OpsFabric provides environment-based approval workflows, maintenance windows, and a complete audit log of every action: who did what, when, on which hosts, and the full result. State assignment changes are versioned with detailed diffs showing exactly what was modified.
"What's your patch compliance rate?"
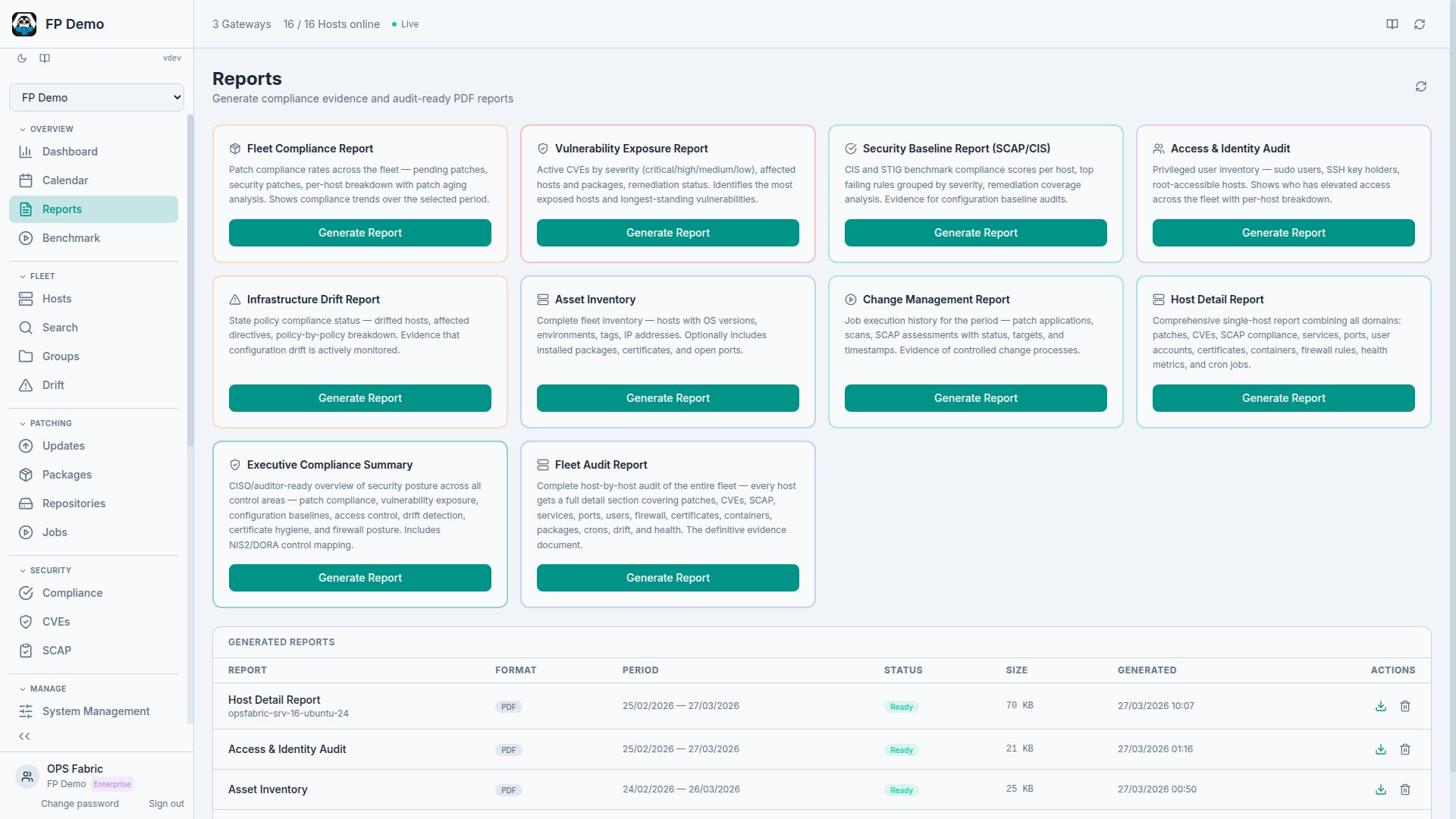
Dashboard views and compliance reports show patch status across your fleet with trend data over time. Export reports for auditors or integrate via the API for automated compliance reporting.
"How do you handle rollback?"
Auditors want to see that you can undo changes safely. OpsFabric supports patch rollback with documented job history, so you can demonstrate that a failed update was reversed and when.
"Is your firewall posture audited?"
OpsFabric audits iptables rules across your fleet, compares them against your declared firewall policies, and flags insecure defaults or unauthorized rules. State profiles enforce firewall baselines and detect deviations.
"Do you monitor certificate expiry?"
Certificate tracking surfaces expiring certificates across your fleet with configurable alerts, so you can prove continuous monitoring of TLS/SSL posture.
The evidence layer
The pattern across all these questions is the same: auditors want to see that controls exist, that they're enforced, and that there's evidence.
Most teams have some of these pieces. They have a patching tool, maybe a vulnerability scanner, maybe a compliance benchmark they run quarterly. The problem is that the evidence is scattered across five different systems, half of it is stale, and none of it is connected.
OpsFabric consolidates the technical controls and evidence into one platform. One place where the auditor can see the asset inventory, the vulnerability management process, the compliance baselines, the access controls, the change management trail, and the drift detection. All connected. All current.
NIS2 and DORA mapping
Here's a practical mapping of how OpsFabric capabilities align with specific directive requirements:
| Requirement | NIS2 | DORA | OpsFabric capability |
|---|---|---|---|
| Asset inventory | Art. 21(2)(i) | Art. 8 | Fleet management, host metadata, OS versions |
| Vulnerability management | Art. 21(2)(e) | Art. 9 | CVE intelligence, CVSS scoring, patch scanning |
| Patch management | Art. 21(2)(e) | Art. 9(4)(f) | Job history with timestamps, approval workflows |
| Security baselines | Art. 21(2)(a) | Art. 9 | SCAP/CIS scan results, compliance scores |
| Configuration management | Art. 21(2)(e) | Art. 9(4)(e) | State profiles, drift detection |
| Access control | Art. 21(2)(i) | Art. 9(4)(c) | User account audit, sudo users, SSH keys |
| Change management | Art. 21(2)(e) | Art. 9(4)(e) | Environment approvals, change calendar, audit log |
| Monitoring | Art. 21(2)(f) | Art. 10 | Dashboard, compliance reports, trend data |
| Rollback capability | Art. 21(2)(c) | Art. 11 | Patch rollback, job history |
| Network security | Art. 21(2)(a) | Art. 9 | Firewall audit, rules library, insecure defaults |
| Cryptographic controls | Art. 21(2)(h) | Art. 9(4)(d) | Certificate tracking, expiry alerts |
What you still need
OpsFabric covers the technical controls and evidence layer. For a complete NIS2/DORA compliance posture, you'll also need:
- A GRC platform for policy documents, risk register, vendor management, and board-level reporting (Vanta, Drata, ServiceNow GRC)
- A SIEM for incident detection, event correlation, and breach notification (Splunk, Elastic, Wazuh)
- People to write the actual policies, manage the risk assessment process, and handle regulatory communication
OpsFabric doesn't replace any of that. It fills the gap between policy and infrastructure. Your GRC platform says "all servers must be patched within 72 hours of a critical CVE." OpsFabric makes that happen and proves it did.
The bottom line
NIS2 and DORA compliance is not a single product purchase. It's a stack of tools, processes, and people working together. OpsFabric's role in that stack is clear: enforce technical controls across your Linux fleet and generate the audit evidence that proves compliance.
You decide the rules. We enforce them. The auditor sees the proof.