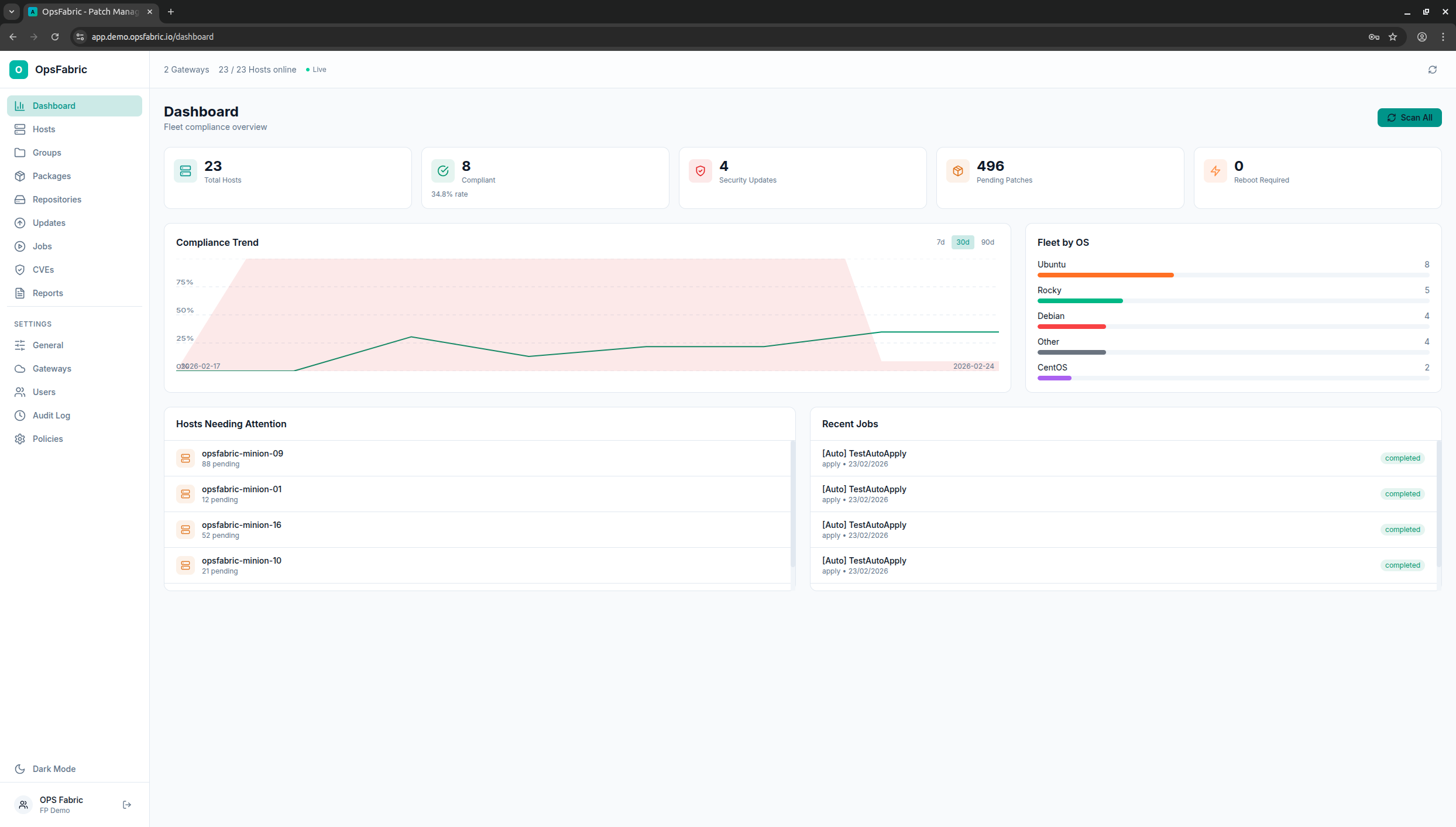
15:25:23 Scan fired across 2 gateways (23 hosts, full scan)
15:25:26 srv-03 complete (1/23) -0 updates
15:25:27 srv-09 complete (2/23) -88 updates
15:25:27 srv-04 complete (3/23) -0 updates
15:25:27 srv-15 complete (4/23) -112 updates
15:25:28 srv-14 complete (6/23) -15 updates
15:25:29 srv-01 complete (10/23) -12 updates
15:25:30 srv-12 complete (15/23) -55 updates
15:25:31 srv-13 complete (19/23) -72 updates
15:25:34 srv-16 complete (23/23) -52 updates
15:25:34 All 23 hosts scanned (2 gateways, 0 timed out)
17:06:33 Package inventory across 2 gateways (23 hosts)
17:06:34 srv-03 546ms 392 packages
17:06:34 srv-02 556ms 569 packages
17:06:34 gateway-2 227ms 584 packages
17:06:35 srv-01 372ms 536 packages
17:06:35 srv-13 511ms 430 packages
17:06:35 10,758 packages inventoried across 23 hosts (avg 468ms/host)
15:26:30 liveness probe - 23 hosts responded in 198ms